Core Principles of the Zero Trust Model
Zero trust requires the model's capabilities to extend throughout an organization and work as an integrated end-to-end strategy and security protocol for the business. Zero trust controls are implemented across numerous foundational elements, acting as a signal point, a protected resource, and an enforcement control plane.
.png?width=790&name=Blog%20Graphics%20(3).png)
The zero-trust security model is designed to fit modern digital transformation needs by uniquely addressing today's cyber trends like ransomware attacks and maintaining security for remote and hybrid workers.
At its core, the zero trust model is guided by the principles of:
- verifying and authenticating explicitly based on all data points
- always assuming the occurrence of a breach, thus, reducing segment access and blast radius and enhancing visibility, defenses, and threat detection
- reducing user access through risk-based adaptive policies and data protection
Trust but verify. As a result, these security models implicitly trust no device or user in the network with legitimate, authorized, or validated access alone. Instead, the model scrutinizes every access request independently before giving access to corporate resources.
How The Zero Trust Model Works
Ransomware is not the only potential threat a small business needs to watch out for. Every user, application, or device is a possible danger to business data.
This outlook is the primary driver of the zero trust model. To gain access to corporate resources, a request must be legitimized by role-based access controls and additional data like user behavioral analytics.
Zero trust requires the model's capabilities to extend throughout an organization and work as an integrated end-to-end strategy and security protocol for the business. Zero trust controls are implemented across numerous foundational elements, acting as a signal point, a protected resource, and an enforcement control plane.
Planning for this security model needs to be based on the requirements of your business, the security stage, and the technologies used.
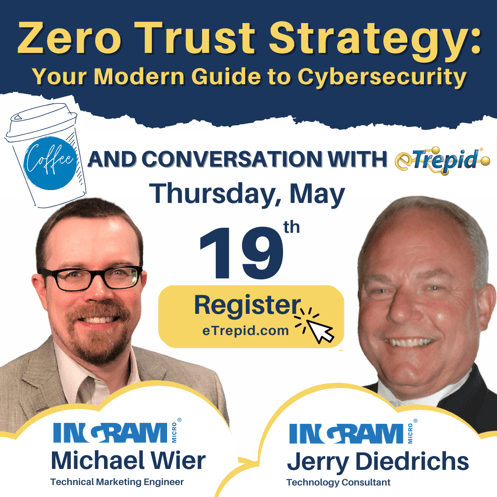
Join Ingram Micro experts, Jerry Diedrichs and Michael Wier during our Coffee and Conversation with eTrepid webinar held on Thursday, May 19th at 11 AM to gain details regarding the Zero Trust model and implementing strategies to modernize your cybersecurity.
Core Principles of the Zero Trust Model
Continuously monitor and validate every user and device trying to gain access as well as determining whether they have the required attributes and privileges. Here are the other key pillars for the Zero Trust Model:
-
Zero Trust Networks
From the perspective that defending your ordinary network perimeter is not enough, the zero-trust network is micro-segmented and distributed into borders defined based on the valuable assets of a company. The micro boundaries make it easier to inspect security and enforce access control. This, in turn, makes blocking, containing, and isolating lateral threat movements or potential threats in the network easy.
-
Zero Trust Identity and Endpoints
Identities define the control plane on a zero-trust model. If any identity tries to access a corporate resource, the model uses strong authentication to identify the identity. This makes sure any access granted is compliant or follows the least privilege access principles.
Related: More SMB should know this about preventing phishing attacks
Data flows to different endpoints, creating a significant attack surface area if the identity is given access. For instance, data can move from on-premises workloads to cloud-hosted servers or from IoT devices to smartphones. In this case, the model monitors and enforces the health and compliance of the data for security during access.
-
Zero Trust Workloads
Many cybercriminals target cloud-based workloads like containers, VMs, and functions. Since these workloads have unique security needs, the granular zero-trust security is tailored to monitor and manage the access of these assets. This is especially critical in a public cloud.
-
Visibility and Analytics
The model uses informed decisions to provide security when access is requested, which requires intensive visibility into the activities within the corporate networks and devices. There is a need to analyze monitors, logs, and correlations constantly. Any data collected is also analyzed from any point of the organization's IT ecosystem to offer complete visibility.
-
Zero Trust Data
The caches of sensitive and valuable data must not only be identified, mapped, and defined for access based on business needs. Instead, the policies governing these types of data must also be defined and enforced consistently across the entire company's ecosystem. This includes mobile devices, workstations, applications, cloud deployments, and database servers.
You should know: What basic security best practices can your SMB follow to protect sensitive business information?
-
Zero Trust Applications
APIs and applications offer the interface where data is consumed. Therefore, there is a need for controls and technologies that ensure in-app permissions are appropriate, user actions are controlled, and secure configuration options are validated.
-
Zero Trust People
Most data breaches occur because of compromised credentials. Therefore, you need a system that provides authentication beyond passwords and usernames. The Zero Trust model uses multi-factor authentication and zero-trust network access to provide extra protection against user credential breaches.
-
Automation and Orchestration
A zero trust model enables your system to detect potential threats or unauthorized activities within your corporate environment. The model's architecture must be integrated with the IT and corporate security infrastructure to support automated, rapid, and scalable incidence response. The collective infrastructure also supports threat hunting, security auditing, and task delegation.
-
Zero Trust Devices
Every device connected to the corporate network is treated as a potential threat or an untrusted device in a zero-trust model. As such, the model must determine whether the device is a threat and isolate those that have been compromised.
The Zero Trust Standard For Businesses
In May 2021, the Biden administration issued an executive order that mandated every US Federal Agency adhere to the NIST 800-207. The mandate was a drive towards implementing the Zero Trust model and a consequence of the nation's increasing number of high-profile security breaches. As a result, this is seen as the standard model for Zero Trust.
It is also the most comprehensive yet neutral standard for organizations and government entities. While it comprises other elements from companies like Gartner's CARTA and has gone through inputs and massive validation from commercial vendors, customers, and government stakeholders, it ensures protection and compatibility against modern attacks for cloud-based remote work infrastructure.
Trust But Verify
Businesses today need a security model that can handle the complexities of digital transformation with ease and adaptability. For instance, the growing mobile workforce increases the need for a security model that protects workers' applications, devices, and data from any location.
This is what the zero trust model does: it assumes threat every time a new request is made, assesses the viability of the threat, and then grants or denies access based on the outcome. Therefore, regardless of location, you can rest easy knowing your corporate resources are always protected.
Gain more information about Zero Trust and see how your security model can adapt to the digital transformation.



.png)
Leave A Comment